Introduction
A detailed evaluation of operating systems fundamentals is essential as the report’s audience constitutes the Oil and Natural Gas Company’s leadership team. Operating System (OS) denotes programs that control computer hardware and offer service for application software. A computer system can be categorized into four parts: a user, the operating system, the hardware, and the application programs. The hardware, consisting of the processing unit (CPU), the input or output, and memory modules that supply essential computational resources to the machine (Silberschatz et al., 2018). Software systems, such as text processors, databases, compilers, and internet browsers, describe how these tools address technical problems to consumers. An operating system also consists of data, hardware, and software. It provides an approach for the proper execution of these elements in a computer system’s operating system. The operating system runs the hardware and controls its operation between various device systems for different users.
Background to Operating System (OS)
An Operating System offers the context in which applications run. Structurally, operating systems differ extensively since they are configured into a wide variety of lines. For a device to start working, for example, whether it is turned up or restarted, a user must execute an initial program. The original software or bootstrap system that a user initiates must be explicit and is installed in firmware on the device hardware. It starts all facets of the machine, from CPU registers, application regulators to program memory.
The bootstrap software independently installs the operating system and runs it. The software must find the OS kernel and boot it into memory to execute the function (Breuer et al., 2018). If the kernel has been initialized and activated, it starts delivering tasks to a computer device and its users. Other utilities occur outside the kernel by machine applications stored in the memory at bootup to become background running programs that operate the whole time the kernel is in use. The first machine system on Linux is “systemd,” and it also runs background programs (Silberschatz et al., 2018). If this process is executed, the system will completely activate, and the machine will prepare for some functions. Another type of disruption is a trigger that is a software-generated pause induced either through a mistake or a particular request by a network interface via a special procedure called a system call. Overall, events are nearly invariably prompted by the presence of an interruption.
Operating systems work within an information systems architecture to execute the intended purpose. In particular, a computer system can be categorized as either a single-processor system or a multi-processor system. A substantial portion of the OS code is devoted to handling inputs or outputs for the system’s stability, efficiency, and different application designs. A general-purpose system contains several devices, all of which share data through a common bus (Breuer et al., 2018). There is just one processor in a memory controller device. As a result, only one procedure may be executed at a point, and then the method is drawn from the waiting queue (Silberschatz et al., 2018). Many multipurpose machines comprise single processor units as they are widely used. Multiprocessing techniques enable linear multiprocessing (SMP), where each peer CPU processor executes all operations, including OS processes and user functions.
Operating Systems are also used in various computing settings to avail services to multiple users. Cloud computing is the most reliable, demanded, and accessible computer system resource for computing power and information storage. In several cases, cloud computing is a conceptual expansion of software solutions, and it utilizes virtual machines as the foundation for its features. Operating systems can use cloud storage for various services, including storing data, disaster management, email, digital workspace, product creation and training, data analytics, and customer-based mobile apps. The Oil and Natural Gas business may use the cloud to provide more tailored services to its customers. Financial institutions can utilize the cloud to track and prevent fraud in real-time. An understanding of the Operating System function allows the assessment report audience to identifies its link to security vulnerabilities as elaborated.
Operating System Vulnerabilities
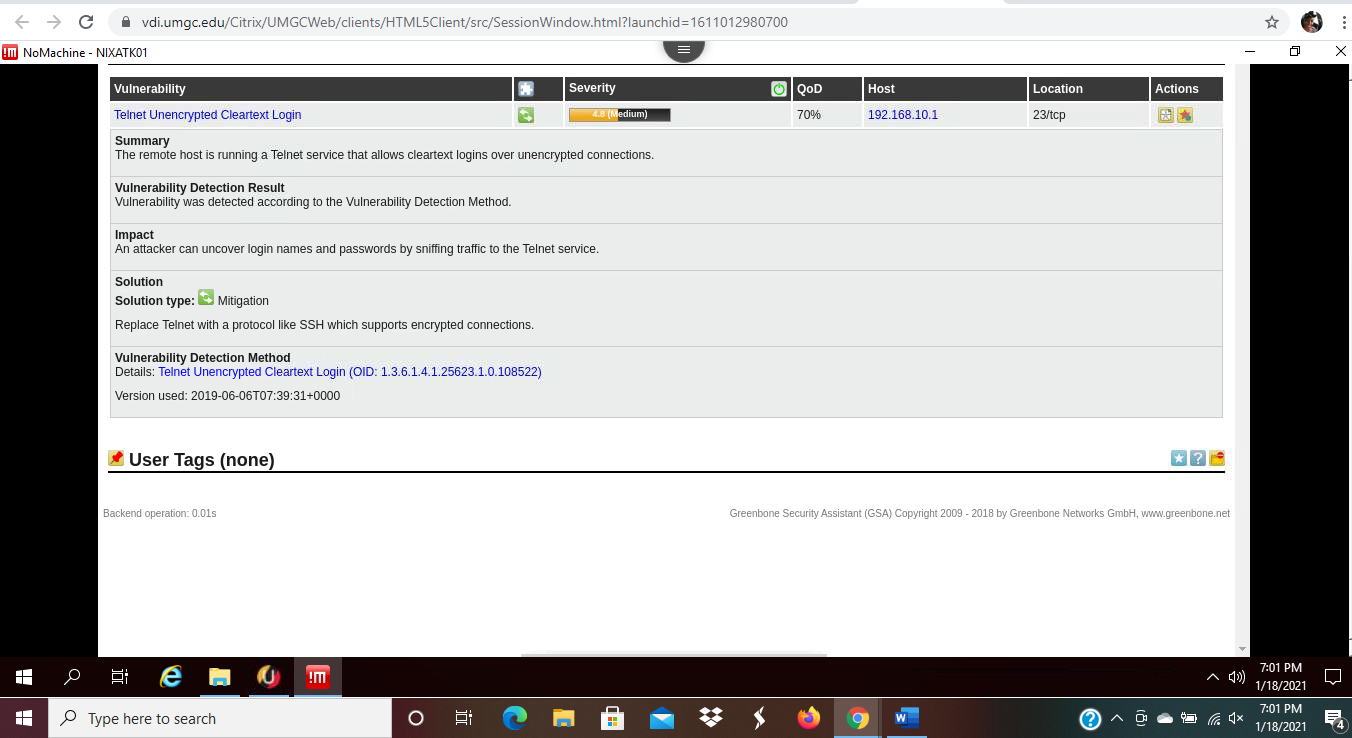
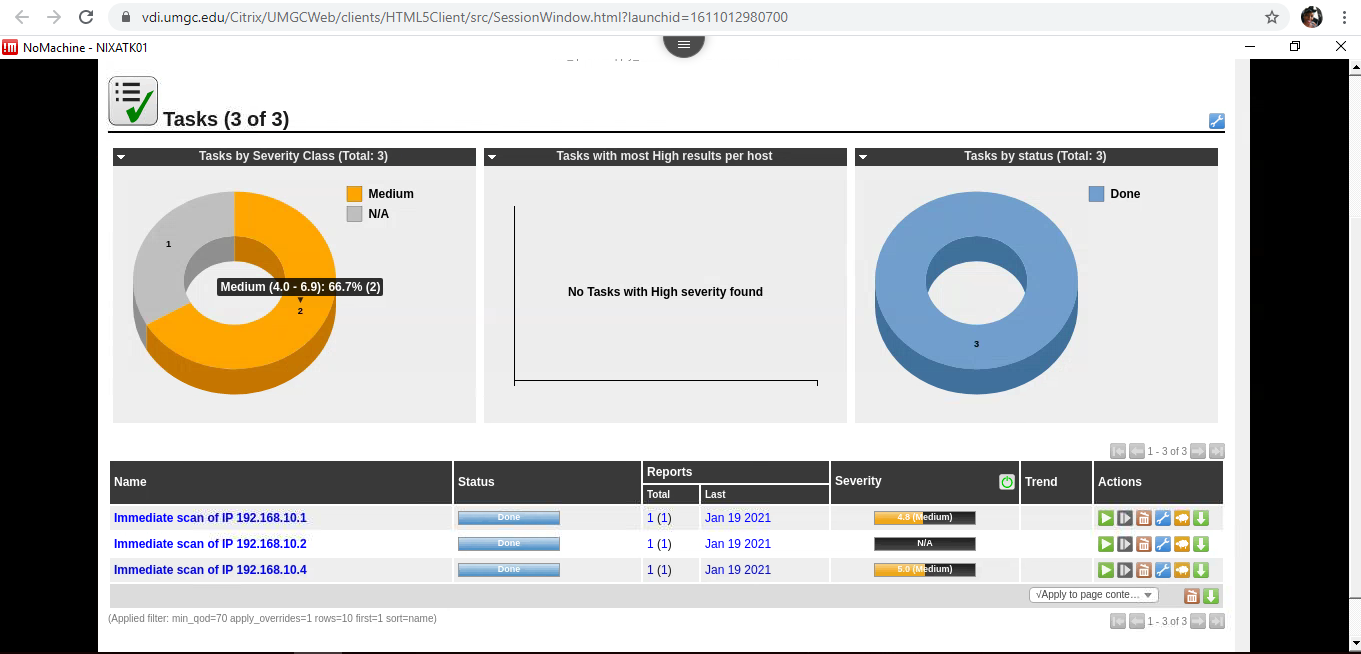
The existing case identifies such OS vulnerability incidents as crashing of database servers and anomalies in the configuration servers and routers. For the Windows OS, administrative vulnerabilities were identified. For instance, Telnet unencrypted cleartext login was listed and the remote host was running services that would allow logins over unencrypted connections as shown in figure 1 and 2. Hence, attackers could easily uncover logins and passwords to the company servers. The issues signify susceptibility to data breaching by unauthorized access to the organization’s OS servers (Gorbenko et al., 2017). In most cases, unauthorized access illustrates insecure identity management. Most OS can have several bugs during service, which may slow down functions or even trigger a breakdown (Jo et al., 2017). Commonly, they exist in the context of CVE-2016-5195, when the error is categorized, which is a simple privilege-escalation of the insecurity instead of the more severe JavaScript vulnerability. To address the vulnerability, it is essential for the company to replace Telnet with a protocol like SSH that supports encrypted connections.
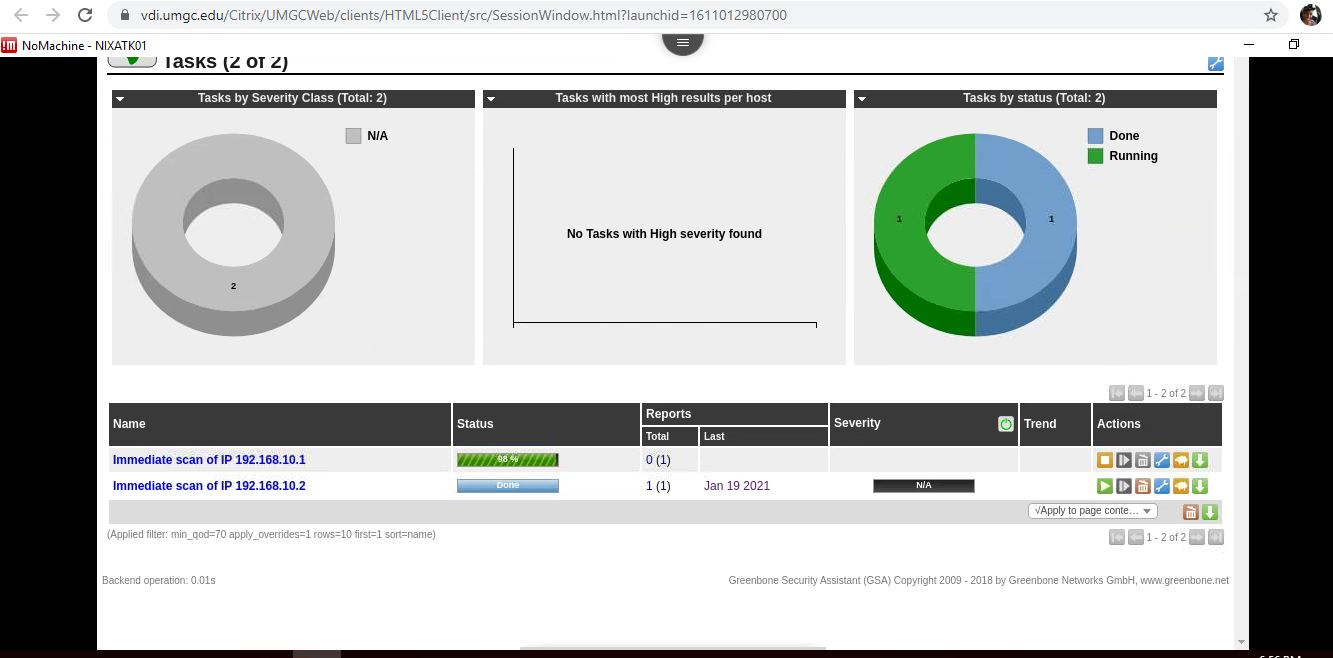
The intent of the attack for both Microsoft and Linux OS is focused on the design of the processing and incorporation of data. In the assessment, further management issues were identified in Linux OS, including scan. The vulnerability was mainly in the DCE/RPC and MSRPC services enumeration reporting as shown in figure 2. The exposure denotes that attackers would use the chance to access and manipulate data about the remote host. Access to this critical information by unauthorized people was easy, and it exposed the company to attacks. As a solution, the company must filter incoming traffic through a different port to identify secure and insecure access.
Vulnerabilities are not limited to computers but can also arise from other portable devices that employees use, including mobile phones and Mac OS. MAC bugs are often defined as linear domains and physical memory machines which code is uniquely programmed in hex format and issued to each user or system unit on a computer system (Gorbenko et al., 2017). Such an OS is more susceptible to mechanical and physical damage. Equally, mobile phones are often considered secure but become susceptible while connected to the Internet (Yesilyurt & Yalman, 2016). The security assessment team could easily access applications in five mobile phones that did not have security codes or passwords restricting access. The employees receive various important communication on mobile phones through messages or such applications as WhatsApp. In particular, important company schedules and financial reports were retrieved from a WhatsApp group, hence exposing important organizational information. Restricted Wi-Fi settings, approving all unfamiliar updates, linking to untrusted servers, and installing applications from unknown sites can also be described as a significant security threat. It is of particular significance that employees must take such safety measures seriously as mobile phones are often exposed to security threats.
Most employees at the organization use android smartphones, which are the most widely available. As open-source software, Android is a Linux-based smartphone use OS built by Google. In particular, the Linux model 2.6 is used for core device resources such as stability, virtual memory, systems integration, host system, and software models. It also serves as an end device between the kernel, operating systems stack generated by the C++ command, and other frameworks. The abstraction layer contains both scheduling and repositories (Yesilyurt & Yalman, 2016). They also require essential libraries, including features in the standard libraries that are built using Java. These modules run on a Linux program for each Android application as per their features. The programs are coded in the Java programming code that can be decoded and manipulated by attackers.
As an organization, different safety awareness systems need to be analyzed to be conscious of and trail the threats. Many security awareness solutions track the network and devices for harmful actions and regulation infringements. All operations shall be communicated to or directly acquired by the security analyst. The framework incorporates data from various locations and utilizes the warning filtering approach to differentiate malicious software. The intrusion monitoring method extends from spyware to hierarchical frameworks that evaluate internet traffic (Gorbenko et al., 2017). The approach can be defined as a security breach and host-based tracking systems. The method is crucial as it helps to evaluate the traffic that is entering the system. The Intrusion Detection System (IDS) is known as signature-based identification and anomaly-based sensors. A portion of the intrusion prevention device can detect breaches (Gorbenko et al., 2017). The IDS will analyze traffic, identify, and avoid vulnerabilities. In the current IT functioning, the existing flaws can be tracked to unsafe programs installed by employees or the lack of a secure user identification system that allowed unauthorized access by hackers who have taken control of the system to obtain the desired applications.
Corporate and government structures experience huge challenges with this intrusion approach. The difficulty can be due to their extraordinarily high level of detail, which benefits various individuals, including politicians, competing entities, nations, and organizations. The current company is no exception as it manages various departments and completes huge financial transactions that are appealing to hackers. Besides, this knowledge is essential because, as marketed to stakeholders, they are willing to achieve a high revenue amount. Structured Query Language (SQL) injection is a detonation where the intruder can add the SQL code to a system form feedback to gain access to the information. It is correlated to an invasion where the end customer inputs a code and special characters and uses them to corrupt data. XML injection is an assault that is used to manipulate or destroy the XML logic program. The infusion can entail modification of the logic, which can support the installation of harmful material. The injection targets the mail server in a manner that would be feasible without using the internet. In the current case, a hacker can easily inject SQL to accessible employee emails.
Identity Management
In cybersecurity debates, programs aimed at controlling access and defining users are deemed crucial. However, authorization management systems and technology have proven challenging. Identity Access Management (IAM) exists to solve this problem, including describing and implementing authentication processes relevant to the most critical business for an organization. Identity management relates to utilizing new technology to handle customer identity details and monitor access to organization services (Ferrari & Thuraisingham, 2020). Identity management aims to increase safety and performance while lowering the costs of handling users and their credentials and personal data. Identity functions are those liable for documenting users within the network so that anybody who has links to them can be correctly verified, with the key pillars of identity protection.
It is crucial for better user authentication that the functions of identities are transparent and that the person who wants to access them can be easily detected. The maximum “minimum privileges” is to be invoked if an individual, by the management of approval classes, receives approval through a notification. Authentication protocols may often be applied to prevent unwanted entry. Authentication is the mechanism through which the device verifies the validity of a user attempting to enter it. Because access control is typically focused on identifying the person requiring access to the resource, authentication is necessary for successful protection.
The documentation that applies to recognizing an individual or object’s authentication confirms identity. It may require checking the validity of a website by a digital certificate or validating an individual’s identification documents. Usually, the system’s way of authenticating an individual user or computer falls into three distinct groups, depending on what is generally recognized as authentication factors: what the user understands and what the user has (Ferrari & Thuraisingham, 2020). Every verification factor shall cover several elements required to authenticate or validate an individual’s identity before entry, authorize a transaction request, sign a contract or other task, give authority, and set up a chain of command.
Another fundamental element to identity security is the idea of authorization, which is deciding a collection of permits given to a particular trust identity. User approval meets authentication in all functional and safety senses. When a machine recognizes a user, it will decide what is best for them to be allowed to do. The system may determine the authorization based on user identities on its own, but in most instances, it needs additional user attributes. Approval should often be achieved remotely by the program used, such as by keeping user privileges in a local archive. The main guidelines used include role-based access control (Chen et al., 2017). The right to privacy plays an exceedingly significant position in people’s lives. And with the growing digitization of the enterprise, a more critical function is likely to be involved.
Educating employees on secure technology use is also important to avoid exposure to the company and employees’ essential documents. The workers can undergo a mandatory workshop detailing the importance of security codes in all their technology devices. The training can elaborate on the need for mandatory logging out of personal accounts when not using computers or mobile phones. The use of passwords will also be reiterated to ensure secure access to personal and business information.
Overall, operating systems play a significant role in a computer system by housing software and hardware components, which execute computerized commands. An operating system controls a computer’s memory, functioning, and hardware and software. In other words, it allows various programs to be installed and to run simultaneously in a machine’s memory. Anomalies to an operating system affect its functioning, and it indicates loss of data or critical software. In the current case, the organization’s systems imply attack hence requires security to protect its Operating System from further assaults that would expose company data. The use of personal identification through password safety is a vital security procedure that can protect the system from external attacks.
References
Breuer, P. T., Bowen, J. P., Palomar, E., & Liu, Z. (2018). On security in encrypted computing. In International conference on information and communications security (pp. 192-211). Springer.
Chen, B., Tan, C., & Zou, X. (2017). Cloud service platform of electronic identity in cyberspace. Cluster Computing, 20(1), 413-425. Web.
Ferrari, E., & Thuraisingham, B. (2020). Digital trust: Trust management in cyberspace. IEEE Annals of the History of Computing, 24(6), 6-7. Web.
Gorbenko, A., Romanovsky, A., Tarasyuk, O., & Biloborodov, O. (2017). Experience report: Study of vulnerabilities of enterprise operating systems. In 2017 IEEE 28th international symposium on software reliability engineering (ISSRE) (pp. 205-215). IEEE.
Jo, H. J., Choi, W., Na, S. Y., Woo, S., & Lee, D. H. (2017). Vulnerabilities of android OS-based telematics system. Wireless Personal Communications, 92(4), 1511-1530. Web.
Silberschatz, A., Galvin, P. B., Gagne, G. (2018). Operating system concepts (9th ed.). Willy and Sons.
Yesilyurt, M., Yalman, Y. (2016). Security on mobile devices and their effects: Estimations for the future. Journal of Security and its Applications, 10(2), 13-26. Web.
