Introduction
Management. Risk issues have become the concern of security management in many organizations to protect the information, which constitutes the needs and requirements of the business. The security information system is a set of policies and management rules formed to maintain a balanced business operation. Information security management is also a type of operation applied to control the business. However, there appear to be risks in this type of management also. Information security is the protection of data from illegal activities.
The major issue of Information security
The major issue related to Information security control is that it reduces productivity but the authorities would like to see information security control as one, which maintains the equilibrium between productivity and Security. This kind of information security control has been considered as an important factor that protects the plans and secrets of high-level organizations such as a government organization or a business organization. The most popular menace to this security system is the lack of confidentiality. Some of the issues identified with confidentiality as follows:
- Hackers.
- Masquerades.
- Unauthorized user activity.
- Unprotected downloaded files.
- Local area networks (LANs).
- Trojan horses.
- Banking networks etc.
A critical component of any business functioning
Risk management, risk assessment, and risk analysis have become a critical component of any business functioning as there seem to be many threats identified in the present-day complex business atmosphere. As far as the risk in information security management is concerned, the risks come in the form of threats listed above. More prominence has been given to continuity and availability in providing information sharing among the business dealings of many organizations and maintenance of official records in governmental organizations. Therefore, risk analysis and management have been given equal attention to that security management.
Risk analysis is the way of analyzing the target field, the target fields include assets as the main concern, which is at risk within the organization. The analysis should identify the threat vulnerabilities, associate these vulnerabilities and affected assets, identify the potential for and nature of an undesirable result, and identify and evaluate risk-reducing countermeasures. Risk analysis also allows the organization to have a grip over its unexpected and expected destiny. A risk analysis is executed by any organization for instance to identify the defenseless area and the result is produced in such a way that the maximum concern is given to eliminate the risk possibility.
It should be noted that a risk analysis or assessment should be carried out within days, not within a week or months. A risk analysis performed within a short period is one of the risk management strategies. Most organizations analyze and manage risk on a cost-effective basis and plan in such a way that time becomes an important concern for them to execute the plan and to avoid the commotion of productivity. The risk analysis and management in terms of calculating the loss expectancy so that a cost-effective risk management plan could be achieved. Given below is the method suggested to calculate the loss expectancy:
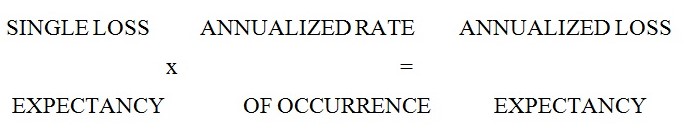
In which the single loss refers to a single vulnerable field of an organization among other expected vulnerable situations, which leads to risk. If risk analysis is said to analyze the reason for risk, risk assessment helps in analyzing the measurement of assets to comprehend the management process, which is again a requirement of risk management. As far as an information system is a concerned asset is considered in the form of “Integrity”, “Confidentiality”, and “Availability”, which means intended information without any undesirable corruption, information maintained with an undesirable disclosure, and information protected along with the availability of the system respectively. Risk assessment on the other hand helps in providing a basis to institute the implementation plan of risk analysis and risk management on a cost-effective basis.
Risk analysis, assessment, and management in information security operations require the work of a team, which has a head to overtake the plan. The head should have the following responsibilities that are:
- Enforcement of state-level security and risk and management policies.
- Establishing and maintaining a risk management program, including a risk analysis process that identifies deficiencies and provides for their corrective action.
- Assigning information asset ownership for all information resources within the agency.
Conclusion
In conclusion, information Security Management is such a risky area that whether it is an organization or Government chances of unauthorized people acquiring the secret information are found in large numbers. With the advent of computerized information security systems, there has been a lot of improvement as well as insecurity existing. Therefore, the risk becomes a strong issue in this field. Based on these notions risk analysis, and assessment formed on a cost-effective basis would help to solve the issue as well as provide the solution for reducing the growth of risks in the future. Overall risk analysis, assessment, and management help in improving the work process and reducing the risk of unauthorized intrusion, and increase protection of the information of an organization.
