A comparison of the usage of information systems in the University of Alberta and the UK protection services (UKPS) – Scotland.
Introduction
The aim of any business or communal establishment is to attract attention to the services it provides and to ensure sustainability by the maintenance of efficient working systems. Information and communication technology (ICT) is a crucial component of any business enterprise, whether big or small. It plays a key role in the management of company operations by ensuring that all members involved are within contact distance from each other as well as assist in the proper organization of company records.
The world is indeed becoming a global village with business exchange and educational activities being carried out through the internet and via satellite systems. In this way, information systems help provide the link between business and technology because the more efficient an organization’s operations are, the more its economic benefits.
Abstract
Various companies depending on their sizes, adopt suitable information systems that help make sensible managerial frameworks. These information systems are vital in ensuring efficiency within the organizations through proper storage and access of data. As a result, gains are made both in terms of company reputation as well as financial benefits. This report seeks to illustrate how two institutions have put the principle of information and communication technology (ICT) into use.
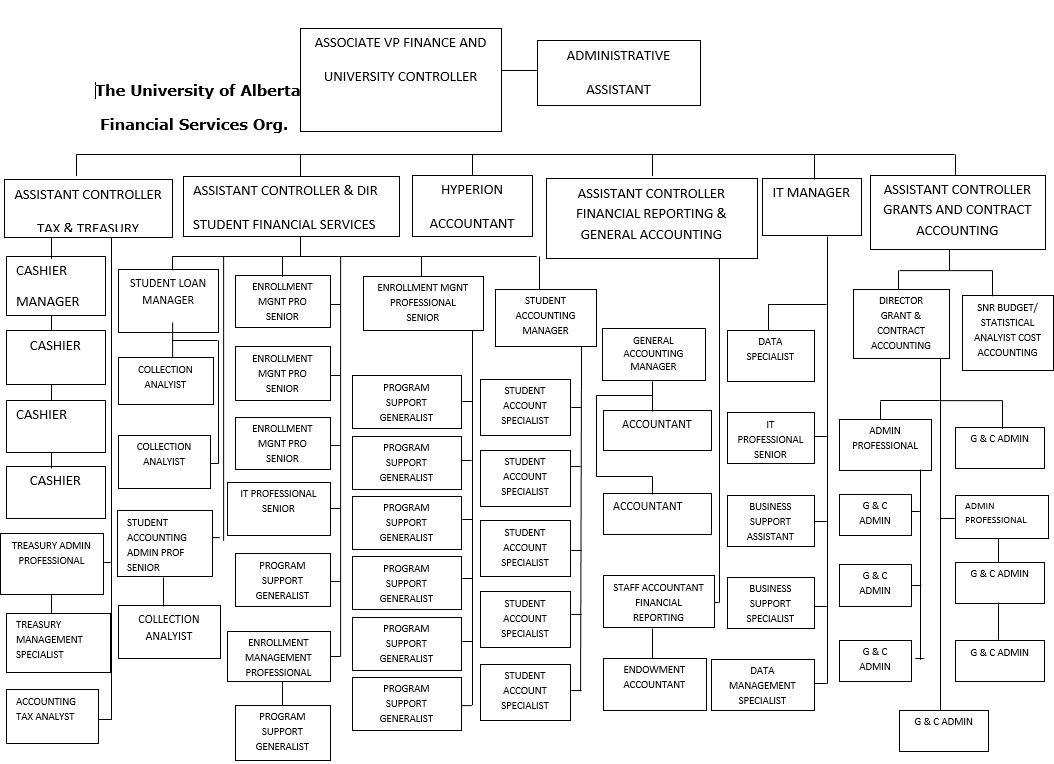
These two organizations are the University of Alberta, which is a large learning institution, and a security company in Scotland-the United Kingdom Protection Services (UKPS). The report follows a basic format where each organization is analyzed independently, starting with a diagram that shows the hierarchy of an administrative part of the entire organization for the larger University of Alberta or an entire company managerial framework for the smaller UKPS.
Various aspects of information systems were studied, including policies, and comparisons have been made in this paper. In the process of obtaining relevant data, this project served the very important role of putting theory into practice by linking information garnered in lectures to its practical application in real organizations.
The University of Alberta
Describe the information systems in use, in general
The University of Alberta has an information system geared at transaction processing, management information, decision support as well as executive information functions. These systems have been established as the west grid whose infrastructures are networking facilities, extensive shared memory, parallel processing facilities, a video conferencing access grid, and even reserves for storage of research data.
This west grid is very important in providing the avenue for researchers to share resources and other elements of expertise. The operation of this information system is modulated by the AICT, and it comprises an SGI Altix XE320 cluster for disseminated memory functions and IBM Power5 and SGI machines for communal memory jobs. The university’s information system also has a General Access Linux Cluster (GALC), which comes in handy for doing large scale parallel computing jobs using the communal memory. Finally, within this system are numerical and statistical servers that host very many geometric, arithmetic, and statistical packages. These five SGI Altix XE250 servers help provide interactivity and group applications.
The information system manpower majorly comprises ICT technicians. These include information officers, operating officers, technical officers, and information security officers. These individuals are responsible for the installation and maintenance of technological equipment that help in enhancing the performance of the organization.
Describe the subsystems in use, specify the functionality of each subsystem
The administrative information systems (AIS) as part of the larger information system are responsible for maintaining proper administrative functions within the college. The systems are majorly PeopleSoft utilities such as payroll, human resource, student, financial, and supply chain records. These systems are continually supported by the IBM Global services, especially in the area of general usage.
The geographic information system (GIS) helps in collecting geospatial data relevant to the running of different areas of administration. For example, the college’s assets, such as already installed infrastructure like transport facilities, have to be constantly monitored for effective management. Other information that is relevant within this system includes data on culture, geopolitical information, and general environmental data.
The Office automation systems (OAS) are very crucial in the maintenance of efficiency within the administration block. Information relevant to this facility is stored in a common database that is accessible using passwords by the relevant authorities.
Describe the networking system in use, specify the technology in use
The university has an operational virtual local area network (VLAN) that helps automate various university-wide services. Access to the VLAN is regulated through an authentication system (Radius server). This radius server configures the users’ port numbers and confines them to a given VLAN, which is in line with the individuals’ needs. As a result, students have their own network, which is separate from the administration’s VLAN.
The networking technology is mainly HP’s 802.1X pro-curve protocol through which the administration can provide either full or limited access depending on the authentication of the user. By this method, guests cannot access secure regions within the network. The college’s Pro-curve networking technology has been actualized using both hardware and software installations. The hardware includes a switch (2524) and a routing switch (9300m series). All installed hardware comes with particular software unique to individual functions.
Describe the Database Management System in use
The university has both network and relational database management systems, which have the DBMS engine as the basic foundation. The engine is supported by various subsystems including the data definition, the data manipulation, the application generation and the data administration subsystems. With both the network and relational DBMS’s users can easily access information from specific data banks within the college though authorization is still a reserve of the management.
Describe the internet connection in use, specify the technology in use
The University of Alberta has both a wireless and wired (Ethernet) system through which authenticated users can connect to the network. There are two wireless systems, the university wireless service and the UAlberta wireless (old system) which both offer connectivity to students and staff. Visitors are also able to access the network via an Eduroam system. In connecting with the greater internet, a fiber optic cable is used since it has the capacity to ferry large amounts of data.
Describe the Microsoft office tools in use
Microsoft office tools are used extensively and more so in the financial services department. Microsoft excel is used in handling all the statistical functions such as payroll and student finance records while Microsoft word is used in recording and presenting more heavily worded documents such as policies and memos. Other Microsoft office tools that are used include Powerpoint and Access which are very ideal in providing key-point presentations either at meetings or via the network system.
Describe the outsourcing policies in use, give advantages and disadvantages
The college’s outsourcing policy bases all the accountability to the office of the vice-president in finance and administration while administrative responsibility falls under resource planning. This policy has the following basic connotations:
- The university will only consider outsourcing provided it improves the efficiency and effectiveness of operations within the college thus allowing more time to the staff to perform the core functions of education and research.
- The university will only approve of proposals to outsource only if they make economic sense.
- The final decisions to outsource will not be made by individuals but rather by an executive planning committee.
This outsourcing policy has the advantage of ensuring efficiency in the usage of the university’s finances and since all major decisions are made by a group, incidents of money laundering and fraud are reduced. The major disadvantage of this policy is that it calls for a step by step analysis of each outsourcing proposal hence slowing down the acquisition of services.
Describe the website in use, and policies in use
The University of Alberta’s website is a corporate dynamic website that provides key background information about the college. Within this site as well is a school sub-site which provides academic information to students within the facility and administrative data to the staff. User satisfaction is encouraged by a feedback operation where visitors to the site can offer opinions about the website and other suggestions that can help improve the services offered online.
Design, development, reengineering, updating, managing and running of the website are guided by the policy that allows only the relevant staff to perform the aforementioned functions. This policy also gives consideration to the opinions of website users especially in the aspect of updating. The website is integrated with the organization’s information system as well as the logistical and bank information system.
However, policy dictates that selective access to certain information is granted to users of the website through an authentication system based on the user’s credentials with the organization. The university offers some online programs to students worldwide. The aspect of language as a barrier has consequently been addressed properly by making parts of the website accessible in a number of languages.
Describe the security policy in use, specify technologies
The university’s website does not gather personal information and only takes it if provided voluntarily. All the information collected is guided by a freedom of information and privacy act which demands that the user be informed of the collection of information, the purpose for which the information is collected and the right of the individual to access the collected information.
While logs within the websites collect information indirectly identifying the user’s location such as the IP address and the domain name, the university does not track or record information regarding individuals and their visits. In cases where the user information is collected, it is the college’s policy not to reveal it to anyone else other than the authorized personnel who are only allowed to use it for legitimate business purposes.
Describe the viral protection policy in use, specify technologies
The university maintains that appropriate anti-viral software is used to scan any new information that enters the system especially via the VLAN as well as through the website. Any recognized malicious operations are immediately terminated and appropriate warning and other security measures taken towards the offending party. Since the university is to a great extent dependent on the information system installations any viral crush-down will lead to a paralysis of operations in the institution. Consequently, the viral protection policy holds that no individual regardless of his/her authority is exempt for the scan whenever sending information through the system.
The University of Alberta has a constitution and policies that govern the running of every sector of the campus. As such, the information and communication department has its own set of rules which guide every operation taking place with the information systems. As far as consultation is concerned, the information systems policy points out that, senior faculty members from the department of computer science and ICT be heavily involved.
These are professors who have vast knowledge of computer technology and therefore are better placed to offer reasonable suggestions as to what information systems can work properly for the institution. The same senior professors assisted by junior colleagues from the department are also taxed with the responsibility of analyzing and designing the information systems that they think best suit the college bearing in mind that the university is growing on a day to day basis. The implementation of the systems is a prerogative of a combination of administrative and ICT staff members.
The ICT members will sit on a board with an administrative team and offer their advice on the best infrastructure that can be installed to adequately maintain a decent information systems network around the college. The same ICT members will then offer a list of equipment providers from which the administrative panel will decide on whose offer would make the best economic sense for the institution. Once new systems are installed, the policy offers the provision that a few individuals from the computer engineering department will familiarize themselves with the system and as such will be responsible for reengineering and maintenance.
The United Kingdom Protection Services-Scotland
Describe the information systems in use, in general
The UK protection services (UKPS) has a specialized information system that offers excellent support for customer service and guidance of company operations. Being a business that directly affects individuals, this system comprises a variety of subsystems including a virtual data ware house, an enterprise resource planning system, a geographic information systems and an office automation system. The office automation system helps in creating an efficient managerial scheme by providing a link between the executive officers and junior administration level officers. Since the UKPS mainly offers services outside the office premises, the geographic information system helps collect geospatial information which is relevant in ensuring a proper record of the covered areas is maintained.
Being an average sized enterprise, the information manpower mainly comprises few ICT technicians whose major role is to ensure smooth running of operations involving the information system as well as its subsystems.
Describe the networking system in use, specify the technology in use
The LAN mainly serves the employees of the company and it is accessible through a regulated password authentication system. In some areas within the company offices, ITU-T G.hn technology has been used to create a high speed intranet. Other regions allow administrative staff into the network via the IEEE 802.1 wireless technology.
Describe the Database Management System in use
A relational database management system has been put in place to help track particular client information whenever need arises. Authorized personnel can link to the data bank to either add or edit information that has been stored in the various databases.
Describe the internet connection in use, specify the technology in use
The company has a local area network (LAN) part of which is wireless. An Ethernet bridge has also been installed to ensure that even the wired part of the system can connect to the wireless part of the system. The wireless part of the network has been configured in such a way that it allows for both internal and external roaming.
Describe the Microsoft office tools in use
Microsoft Word, Excel, Access and Powerpoint are used extensively within the company. Word is very important in processing company documents and client applications while Excel is mainly used in the financial department in keeping payment records and analysis of company expenses as well as profits. Powerpoint is very useful in offering presentations illustrating the company’s progress.
Describe the outsourcing policies in use, give advantages and disadvantages
The company has an outsourcing policy that has been designed to help reduce the information security risks that are normally related to outsourcing. This policy covers every level of the administration. This policy operates under two main axioms:
- The commercial benefits must balance with the risks involved in the outsourcing process.
- The risks associated with outsourcing must be reduced to the bare minimum through use of legal, physical and managerial controls.
Once a decision has been reached at to outsource, a suitable service provider is identified and a contract is signed by both parties. This contract clearly defines each party’s responsibility to the other. After a risk assessment has been carried out, extra security information is included within the contract. This information includes regulatory and other third party responsibilities including data protection and privacy legislation.
Describe the website in use, and policies in use.
The UKPS website is a corporate dynamic (automated) site with information being generated periodically. It provides important background information about the company and enlists services offered by the organization. Some pages within the website serve the purpose of brand building by offering testimonials and listing the professional qualifications of employees. The design, reengineering, updating, managing and running of the website is mainly outsourced from companies that specifically deal with websites.
Since this company operates as a member of the service industry, regular updating and redesigning of the website is mandatory in order to attract new clients. UKPS-Scotland offers security services to residents of the country and does not exactly sell products that other people around the world could purchase online. Therefore, the need for language translation on the website is not called for.
Describe the security policy in use, specify technologies
The website offers ways of contacting the company management but does not at any time demand for visitor’s contact details. The company has software programs that can monitor traffic in the web and in the process collect information which can indirectly identify the user such as the IP address and the domain name. This information is however for administrative purposes only and is at no time stored with the aim of keeping records on an individual’s visits.
Describe the viral protection policy in use, specify technologies
The company has a policy that any data that enters into the system be properly screened using appropriate software. This data can originate from within the LAN or from the internet through the website. The antivirus software is supposed to lock out any malicious programs attempting to find way into the information system structure.
The UKPS is a small institution and its policy framework covers every area of operation of the institution with some very minor specifications on individual departments. Since the institution has a small department that deals with ICT, the staffs in this area are the responsible for analysis of the system and offer suggestions as to what changes need to be made. These same members of staff will sit with the senior administrators and pitch their ideas as well as offering suggestions on the best equipment providers. The administration will then study the list of suppliers both from within the country as well as abroad and then decide on which purchase would make more economic sense.
Once the new system has been installed, the staffs in the department of ICT will be responsible for the maintenance and reengineering of the system. The policy also holds that should there be need for individuals to be trained specifically to handle the new system, the company will finance this training provided the individual comes back to work for a period of time not less than two years. This individual should ideally be from the company’s ICT department.
Give comparative studies of the two systems
This project has effectively analyzed the information systems usage in two companies; the University of Alberta and the UK Protection Services-Scotland. While it may be hard to give a direct comparison of the two organizations judging from their difference in size, it is interesting to see the similarities in the application of ICT technology. The following key points were noted:
The University of Alberta’s network system is mainly a west grid which comprises an SGI Altix XE320 cluster for disseminated memory functions and IBM Power5 and SGI machines for communal memory jobs. Aside from these, there is also a general access Linux cluster which streamlines parallel operations when the shared memory is under use. This university also has three other subsystems; a geographic information system, an office automation system and an administrative information system. UKPS on the other hand has a less fancier system. Its major component is the GIS since the company mainly deals with security services around the country. However, for effective running of the company an office automation system is also used.
The networking system for the university is essentially a VLAN regulated by a radius server which operates by confirming password authentication. It is a very efficient system in terms of keeping unauthenticated users at bay. As far as DBMS is concerned, the university has both relational and network systems in place. UKPS has a LAN networking system which is accessible by authorized staff via the IEEE 802.1 wireless technology. The company’s database is exclusively relational and staff can login to update information that is stored in the database.
The university has both a wired and wireless internet connection. Students and staff of the college can gain access to the wired connection via various ports spread out around the campus. The wireless system is accessible within the radius of the institution. An Ethernet connection helps link the wired connection to the wireless system. UKPS has a wireless internet connection with an Ethernet bridge connecting the wired LAN to the wireless system.
Both the University of Alberta and the UKPS use three major Microsoft office tools extensively. These are Word, Powerpoint and Excel. Excel plays a major role in the financial departments of both institutions where it is used to process statistical and numerical data while Word and Powerpoint are used to work on worded data.
The outsourcing policies of both companies mainly serve as guides to ensure that imported services make economic sense to the establishments as well as ensure that the risks involved with outsourcing are reduced to a bare minimum.
The University of Alberta’s website is corporate dynamic. There is also a school sub-site entrenched within the primary website to serve the interests of students and staff. Design, reengineering and updating of the website are activities exclusively left to authenticated staff. UKPS also has a corporate dynamic website with some pages left out to handle the task of brand building. Updating and reengineering of the website is guided by a policy that categorically allows for these functions to be outsourced.
As far as security and privacy is concerned, both websites offer options for visitors to live their contact details but this is only on a voluntary basis. The two companies also have software that keep track of web traffic and can collect information which can identify the users albeit indirectly such as the IP address and domain name. This information is however collected for administrative purposes only.
The viral protection policies of both institutions demand that any data which enters the systems be adequately screened from various viral applications. These policies do not offer leeway for anyone including staff members to by-pass the scans and as such all information originating from the LAN and the larger internet is subject to screening.
The University of Alberta has its own in-house computer technology specialists who deal with the process of consultation, implementation, running and reengineering of the information systems that have been installed. These ICT professionals however have to work hand in hand with administrative officers especially in the finance department when it comes to purchasing of new equipment. UKPS-Scotland as well has a small team of professionals in the ICT department who like their counterparts in the university are responsible for consultation, implementation and running of the information systems. They also have to work together with the administrative officials and more so those in the finance department whenever purchases or hiring has to be done.
Conclusion
While this may have been a class assignment, it has helped provide further education on how Information systems are used to achieve great gains both in small and large enterprises. This report has listed some of the major aspects of network systems which have been installed in two organizations and has even gone ahead to give an analysis of the technology and policies involved. In conclusion, it is worth noting that the world is adopting technology at a very impressive rate and that all sectors including business and commerce will eventually rely entirely on technological advancement for effective management. This report has illustrated how network systems are serving the key role of maintaining efficiency in both micro and macro-enterprises.
