Introduction
The art of communication is effective when conducted clearly within the organization’s encode and decode channels. Organizations function best when this system is perfect. Therefore, successful organizations manage information continuously. The practice of information management involves the science of processing information to facilitate informed decision making among managers. However, the channels of this information should be protected to ensure protection of the organization’s private information that may lead to the unwanted third party interference.
The Arden Hill Hospital has very weak information security system with a series of loopholes that makes it vulnerable to access by third parties. Thus, this analytical treatise attempts to present a secure, easy to use and reliable information management system for the Arden Hill Hospital to stop the current information insecurity in the hospital’s information data system. The report suggests establishment of an information security policy, enforcement of the information security policy, provision of support tools for securing information, plugging security holes, and hiring a HIPAA security compliance administrator for the hospital.
Literature Review
With the recent developments in the information security system, programs have been designed that automatically prompt the staff on password updates, security alerts, and daily reminders of the need to be cautious when accessing the system. The internal and external reporting channels are then cascaded down to the rest of the organization structures. The two structures differ in the sense that there is an indication of unity, integration and internal orientation in line with the security results.
In information system implementation planning strategy, culture defines all aspects of a business, both internal and external relationships. First, the management should consider having an intranet for the hospital. This is a secured internal or private network of an organization that connects all computers to increase the access to the internet. An intranet is restricted to an organization and its associates (customers, employees, members and suppliers among others) and is protected from unauthorized access by security systems and firewalls. Such security encryption puts a stop to abuses of the system like social networking, inapt use of the web, among others.
Generally, a risk is regarded as a negative factor in the introduction of new technology because of its associated downside exposure to unrealized benefits, technical; performance shortfalls, time slippage, cost overruns, and withdrawal of the staff who may feel sidelined. It is imperative to have a good strategy to manage the risks associated with the adoption of new concepts such as technological efficiency. Estimation and evaluation of risk is an assumption that it is possible to draw logical conclusions regarding the chance of a risk occurring, as well as the possible effect of that risk. Risks can also be categorized as a short-term or a long term risk. Determination of short term risks assists in mitigating long term effects which may result from neglected short-term risks.
Ethics can be applied in any profession. Basically, ethics denote sets of laws or moral systems that provide a basis for discerning whether an action is correct or erroneous. Therefore, members of a profession can come up with ethical principles that guide them when carrying out their duties. As it happens in other organizations, there should be laid down structures formulated in to keep staff in healthy and stable mind in their duty of serving the Hospital’s interest through regulatory ethical communication models. These models define expected behavior, procedural patterns, and response to every deviation.
In order to give an information security policy the implementation strength, the components should be communicated to the staff and a hard copy of the policy hanged on all the rooms in the hospital. In this way, none of the staff will argue on the basis of ignorance whenever security breach is identified. In order to implement this policy, the hospital should hire an information security professional to offer periodic trainings on cultured security systems as a component of employee orientation training to include direct effects of the policy on staff’s work life.
The hospital should put out most of the documents such as policies, procedure manuals and new rules through the intranet Web pages. This saves the company costs relating to printing, maintaining and circulating such documents. Also, an intranet makes it easier for communication across the organization, especially on security alerts. Secondly, the management should consider using internet tools such as VoIP and Groupware. These technology tools would provide a good avenue for interaction between the information security support, the staff members and the ease of integrating secure administrative applications of the hospital.
Analysis and discussion
In order to implement the secure information system, the management should introduce a compulsory periodic training of the staff on the vital aspects of system protection. An information system that adopts a participatory approach in design internalizes the aspect of responsibility of the staff since each will have first hand information on the importance of avoiding negligence. This aspect will eliminate the ignorance exhibited by some of the staff who are not careful with their passwords and easily give them out. Through participatory information system training, the staff will be equipped with relevant and necessary skills for taking personal responsibility for every information security breach originating from their computers. In the participatory information design model, the staffs are liberated to understand how the system works and the consequences of carelessness on their part.
The hospital should adopt a strict information security policy that establishes the acceptable behavior guidelines. Specifically, the HSO should establish a clear relevant and concise security system for the employees on the need for protection of their passwords and accountability for every access to the system using these passwords. In addition, the system should include physical security of the licensing network system that prompts the administration of every download, origin of the download, and the person responsible for that computer.
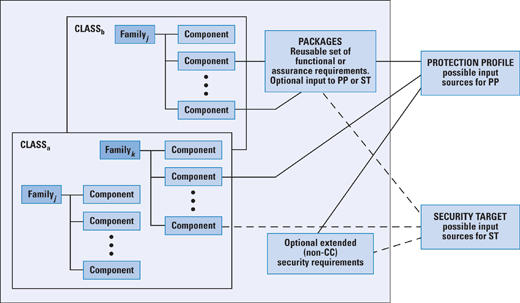
In order to make the policy effective, the management should appoint a chief information security officer who is expected to hold meetings with the CEO at least twice in a month to confer on the vulnerabilities of the hospital’s information management system. In addition, the information security officer and his or her team should be given the necessary information management tools such as password trackers, system monitors, and network reviewers to be in a position to prevent a possible breach of information security and offer an efficient and immediate response to an identified threat. When this policy is implemented, the issues of internal and external information management system compromise will be minimized. This is summarized in the diagram below.
Conclusion and Recommendations
Conclusively, the hospital should concentrate on developing a stringent information security that will protect the hospital’s information system from access by third parties that are not authorized. When these are implemented properly, the hospital will be in a position to avoid information security lapses it currently experience. There is a need for staff members to adapt quickly to proposed changes in the information management system in order to ensure that a participatory approach is acceptable to them.
